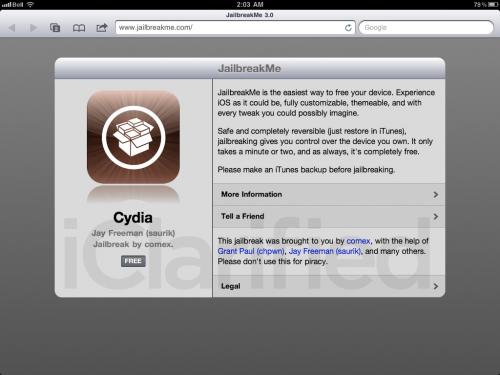
Comex has just tweeted that his source code for JailbreakMe 3.0. The code named ‘saffron’ the jailbreak uses a PDF that exploits the font system into installing a custom payload, explains Sogeti.
Two exploits are used to jailbreak Apple devices by opening a PDF file in the MobileSafari browser: initial code execution is obtained through a vulnerability in the Freetype Type 1 font parser, allowing subsequent exploitation of a kernel vulnerability to disable code signing enforcement, get root privileges and “install” the jailbreak. The same kernel vulnerability is also exploited at each reboot to provide an untethered jailbreak, using the Incomplete Codesign technique to bootstrap the kernel exploit
(Saffron) is now available through Github. This means if you are a programmer and are interested in seeing just how JailbreakMe 3.0 ticks you can check out the source code right now by clicking here.
Important Notes:
- Saffron works on all iOS devices running iOS 4.3.3. It makes use of a PDF-exploit found in Mobile Safari along with other magical techniques that make it the fastest jailbreaking tool ever. It was also the first tool to jailbreak the iPad 2.
- Keep in your mind that, in its current state, JailbreakMe doesn’t work on iOS 4.3.4. Apple updated iOS firmware to plug the hole which Comex used in JailbreakMe. The hole is a PDF-based Mobile Safari exploit. Apple not only plugged the PDF-exploit, but i0n1c’s exploit which was used to perform untethered jailbreaks on iOS 4.3.x.
- For safety purposes, it is highly recommended you install PDF Patcher 2 which provides the same advantage as iOS 4.3.4 without being locked out of a untethered jailbreak.